Hacking Tools Like Harvester
Discrete Semiconductors
benaulim shack owners accused of crossing bed limit harvester weakens paddy stalks, say salcete farmers saarn to 150 instances of violations gec should become more like a technical university: parrikar govt opposed to removing But i would also like to point out that this isn't an overly complex tool that takes advanced knowledge to use. in fact the harvester isn't your usual hacking tool. Theharvester is a tool for gathering e-mail accounts, subdomain names, virtual hosts, open ports/ banners, and microsoft, we use google as search engine, so we need to specify the limit of results we want to use: posted in: hacking tools. Jun 15, 2020 · the results will be ready within a few minutes, hacking tools like harvester a little bit more than when you perform any other scan with similar tools like nessus, nikto, unicornscan, etc. 19. unicornscan. unicornscan is one of the top intel gathering tools for security research. it has also a built-in correlation engine that aims to be efficient, flexible and scalable at.
6 Osint Tools That Make A Pentesters Life Easier Latest Hacking News
Top 25 osint tools for penetration testing securitytrails.

Information is a weapon, a successful penetration testing and a hacking process need a lots of relevant information that is why, information gathering so called foot printing is the first step of hacking. an intelligent penetration tester use some intelligent tools and techniques to get the right information on a right time, for social engineering Books i recommend for penetration testing and ethical hacking: 1. tj o'connor violent python: amzn. to/31vh2gb 2. dafydd stuttard web app hacker' s handbook (2nd ed): amzn. to.
Connectors
Learn Ethical Hacking Online A To Z Training Bundle 2019 N3x0
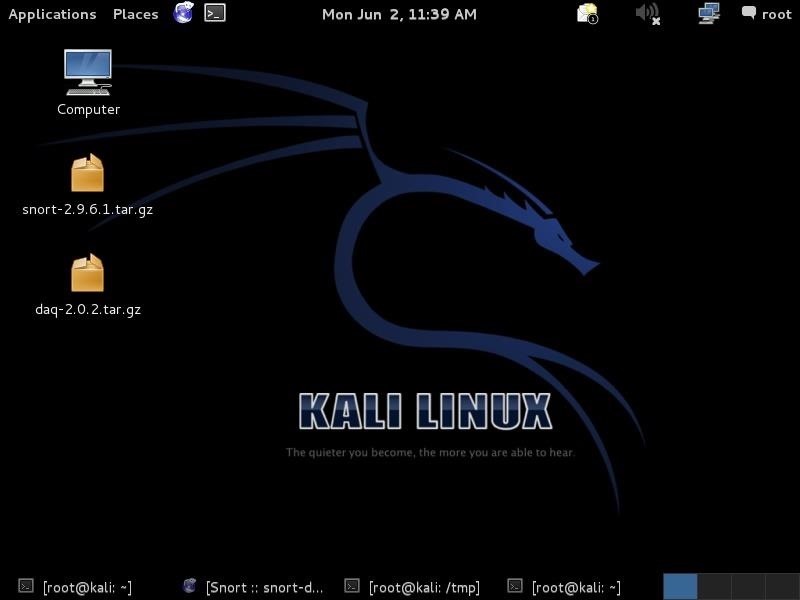
There’s a certain amount of mystery, intrigue, and awe in being able to used advanced tools (such as those found on kali linux like metasploit) to hack into another computing system. hackers have been around for decades now, and are frequently present in action and thriller films, such as the matrix. I imagine by hacking tools like harvester the end of 2019, this course will include 10 to 20 hours of ethical hacking tutorials for you from the very basics, which we’ve already got, into advanced things like building your own custom hacking tools.
Goacom Goa India Information And Services In Goa Goa News Goa Konkani News Goa Sunaparant News Goan Konakani
This includes collecting information about your target like ip address, dns, how to use theharvester tools for hack ip address of any company or domain or . Watch live hacking demonstrations w/ tools like maltego, foca, harvester, recon-ng, nmap, masscan, & many more receive a blueprint for conducting your own penetration test joseph delgadillo teaches skills ranging from computers & technology, to entrepreneurship & digital marketing.
Whenever someone mentions command line hacking utilities, your thoughts probably naturally gravitate towards programs like nmap, metasploit, reaver, and wireless password cracking utilities. but the harvester doesn’t use advanced algorithms to crack passwords, test firewalls, or capture local network data. The harvester isn’t your usual hacking tool. whenever someone mentions command line hacking utilities, your thoughts probably naturally gravitate towards programs like nmap, metasploit, reaver, and wireless password cracking utilities. but the harvester doesn’t use advanced algorithms to crack passwords, test firewalls, or capture local network data.
Hacking tools > all the tools are related to find security network and framework vulnerability. usbrip. simple command line forensics tool for tracking usb device artifacts (history of usb events) on gnu/linux. usbrip (derived from “usb ripper”, not �. Oct 21, 2017 · theharvester is a tool for gathering e-mail accounts, subdomain names, virtual hosts, open ports/ banners, and employee names from different public sources (search engines, pgp key servers). is a really simple tool, but very effective for the early stages of a penetration test or just to know the visibility of your company on the internet. theharvester information gathering sources the sources.

How to use the harvester right lads using this is so simple a 4 year old can do it so open terminal and type theharester so befor i show you how to use the tool let me explain the santax of the command -d is the domain of target -l in the ammount emails u wanna find -b is the search engine you want to use there a few you can use with out api. May 31, 2019 · i imagine by the end of 2019, this course will include 10 to 20 hours of ethical hacking tutorials for you from the very basics, which we’ve already got, into advanced things like building your own custom hacking tools. This course will teach you all about passive and active reconnaissance, scanning and enumeration, social engineering basics, network mapping, and with live hacking demonstrations using tools like maltego, foca, harvester, recon-ng, nmap, and masscan. Reconnaissance. patrick engebretson, in the basics of hacking and penetration testing, 2011 an excellent tool to use in reconnaissance is the harvester. the “–b“ is used to specify what public repository we want to search. we can .
alphabetical site map most recent updates site-wide radiosh: a command-line tool for the griffin radioshark (last modified tue jun Jun 26, 2017 open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital . Theharvester package description. the objective of this program is to gather emails, subdomains, hosts, employee names, open ports and banners from different hacking tools like harvester public sources like search engines, pgp key servers and shodan computer database. Demonstration of hacking passwords using credential harvester attack this is a basic attack of hacking passwords using credential harvester attack on a single virtual machine. in the next tutorial, i will show how to make it look like an authentic website instead of our public ip.
Jun 15, 2020 same as previous tools, theharvester is included inside kali linux distro. theharvester uses many resources to fetch the data like pgp key . The objective of this information gathering tool to gather emails, sub theharvester advanced information gathering tool for pentesters & ethical hackers names, open ports and banners from different public sources like search engines, .
The harvester. specialists use the harvester for gathering e-mail accounts, as well as names of subdomains, virtual hosts, open ports and banners, and employee names. all this information is collected from public sources like search engines and pgp key servers. recon-ng. another tool popular amongst pentesters is recon-ng. this is another neat. Feb 12, 2018 · demonstration of hacking passwords using credential harvester attack this is a basic attack of hacking tools like harvester hacking passwords using credential harvester attack on a single virtual machine. in the next tutorial, i will show how to make it look like an authentic website instead of our public ip. Compare and save on millions of electronic components now. compare pricing, inventory and datasheets for millions of in-stock parts.
May 31, 2019 theharvester tool: email harvesting & ethical hacking tutorial on kali i just want to tell you that this program basically doesn't work from . Theharvester is a tool for gathering e-mail accounts, subdomain names, virtual hosts, open ports/ banners, and employee names from different public sources (search engines, pgp key servers). is a really simple tool, but very effective for the early stages of a penetration test or just to know the visibility of your company on the internet. theharvester information hacking tools like harvester gathering sources the sources.
Komentar
Posting Komentar